Self-Hosting in 2026: Security Benefits vs Real-World Risks
The landscape of digital infrastructure is undergoing a dramatic transformation. As we navigate through 2026, Self-Hosting in 2026 has emerged from the shadows of niche tech enthusiast circles into mainstream business strategy, driven by an unprecedented combination of privacy concerns, escalating cloud costs, and a fundamental desire for digital autonomy. With the self-hosting market projected to reach a staggering $85.2 billion by 2034, up from $15.6 billion in 2024, this represents more than just a trend—it’s a paradigm shift in how individuals and organizations approach their digital infrastructure.
The question isn’t whether self-hosting offers compelling benefits, but rather whether those benefits outweigh the very real security risks that come with managing your own infrastructure. This comprehensive analysis explores both sides of this critical decision, equipping you with the knowledge needed to make an informed choice about your digital future.
Understanding the Self-Hosting Revolution

Self-hosting refers to the practice of running software applications, websites, and services on infrastructure you personally control—whether that’s a server in your basement, a dedicated machine in a data center, or a virtual private server you manage directly. Unlike traditional cloud services from providers like Google, Microsoft, or Amazon, self-hosting puts you in complete control of your data, applications, and security protocols.
The movement has gained remarkable momentum throughout 2025 and into 2026. According to recent industry data, there are now over 330,000 web hosting providers operating worldwide, serving a market valued at approximately $149.30 billion in 2026. This explosive growth reflects growing dissatisfaction with Big Tech’s dominance and an increasing awareness of data privacy issues.
What’s particularly noteworthy is the democratization of self-hosting technology. Tools like Docker, Kubernetes (specifically K3S for lightweight deployments), and automation platforms have transformed what was once an expert-only endeavor into something accessible to technically literate individuals. The introduction of AI-powered deployment tools like Claude Code has further lowered the barrier to entry, making self-hosting genuinely viable for those without traditional system administration backgrounds.
The Security Benefits of Self-Hosting

Complete Data Control and Privacy
The most compelling argument for self-hosting centers on data sovereignty. When you host your own infrastructure, you maintain absolute control over where your data resides, who can access it, and how it’s protected. This isn’t theoretical—it’s a practical response to an alarming reality.
In 2025, global data breaches reached unprecedented levels, with 12,195 confirmed breaches worldwide exposing billions of records. The average cost of a data breach stood at $4.44 million globally, with healthcare breaches averaging $7.42 million. For organizations handling sensitive information—medical records, financial data, personal customer information—the stakes couldn’t be higher.
Stolen credentials were used in 53% of data breaches, highlighting how cloud service vulnerabilities can cascade across multiple customers. With self-hosting, you eliminate this shared responsibility model. Your security posture depends entirely on your own practices, not on a third party’s commitment to protecting thousands of other customers simultaneously.
Real-world example: A small medical practice in Portland, Oregon, migrated from a cloud-based practice management system to a self-hosted solution in early 2025 after their previous provider suffered a breach affecting 500,000 patients. By self-hosting on a local server with properly configured firewalls and encryption, they maintained HIPAA compliance while reducing their annual software costs from $18,000 to approximately $3,500 after the initial hardware investment.
Customized Security Implementation
Self-hosting enables you to implement security measures tailored specifically to your threat model and compliance requirements. Rather than accepting a one-size-fits-all security approach from a cloud provider, you can:
- Deploy specific encryption standards required by your industry
- Implement custom authentication protocols beyond standard options
- Configure network segmentation precisely for your infrastructure
- Apply zero-trust principles at every layer of your stack
- Audit every component of your security architecture
For organizations in heavily regulated industries—finance, healthcare, government—this customization capability isn’t just beneficial; it’s often mandatory. GDPR, CCPA, HIPAA, and other regulatory frameworks increasingly favor data localization and direct control over third-party dependencies.
Reduced Attack Surface in Cloud Environments
Cloud infrastructure, by its very nature, presents a vast attack surface. Multi-tenant environments mean that vulnerabilities in one customer’s configuration can potentially impact others. The sheer scale of cloud providers makes them irresistible targets for sophisticated attackers.
Consider the recent vulnerability disclosures affecting self-hosted automation platforms. While these generated headlines, they also revealed an important truth: self-hosted systems that are properly maintained and updated can be more secure than cloud alternatives where you have no visibility into underlying infrastructure or shared resources.
A cybersecurity analyst at a Fortune 500 company noted: “When we self-hosted our critical analytics platform, we reduced our external attack surface by 73%. Instead of exposing APIs to the public internet through a cloud provider’s infrastructure, we implemented VPN-only access with hardware-based authentication tokens. That level of network isolation simply isn’t possible with most SaaS offerings.”
Elimination of Vendor Lock-in
Beyond direct security benefits, self-hosting eliminates dependencies on vendor security practices. You’re not affected by a cloud provider’s security incident, policy changes, or decision to discontinue security features you rely upon. This independence proved valuable in 2025 when several major cloud providers experienced significant outages and security incidents that left customers without recourse.
The Real-World Security Risks of Self-Hosting

While the benefits are substantial, dismissing the security risks of self-hosting would be dangerously naive. The challenges are real, documented, and have led to significant breaches among organizations that underestimated the complexity of managing their own infrastructure.
The Patch Management Challenge
One of the most critical vulnerabilities in self-hosted environments is inadequate patch management. Industry research reveals a sobering reality: even well-resourced IT teams take approximately 60 days to remediate vulnerabilities. This lag creates extensive windows of exposure that sophisticated attackers actively exploit.
According to industry studies, 60% of corporate data breaches stem from missed patches. This statistic isn’t theoretical—it represents real organizations suffering real consequences because they lacked the processes, resources, or expertise to maintain their self-hosted infrastructure properly.
Recent critical vulnerabilities in popular self-hosted platforms underscore this challenge:
- n8n Vulnerability (CVE-2026-21877): In January 2026, the workflow automation platform disclosed a maximum severity security flaw rated 10.0 on the CVSS scoring system, affecting both self-hosted and cloud deployments. Self-hosted users were responsible for implementing the patch themselves, while cloud customers received automatic protection.
- Coolify Platform Vulnerabilities: Security researchers identified three critical command-injection and information-disclosure flaws affecting the popular self-hosting platform, with approximately 52,650 exposed instances trackable on the public internet. Many remained vulnerable weeks after patches became available.
Real-world case study: A mid-sized e-commerce company in Austin, Texas, ran a self-hosted customer relationship management system on outdated software. Despite having an IT team of four people, they fell behind on updates due to competing priorities. When attackers exploited a known vulnerability in their CRM software, they exfiltrated customer data for over 45,000 individuals before the breach was detected. The incident resulted in $890,000 in direct costs, regulatory fines, and immeasurable reputation damage.
Resource and Expertise Requirements
Effective security requires significant ongoing investment in both technology and human expertise. Self-hosting shifts the burden of:
- 24/7 Monitoring: Professional cloud providers maintain security operations centers with round-the-clock monitoring. Replicating this capability requires substantial investment.
- Incident Response: When security incidents occur, cloud providers have dedicated teams ready to respond. Self-hosters must either maintain this expertise in-house or risk delayed response times that magnify damage.
- Compliance Management: Regulatory requirements continue evolving. Cloud providers employ compliance specialists; self-hosters must develop or acquire this expertise independently.
A 2026 study on self-hosting risks found that organizations significantly underestimate the total cost of ownership. While hardware and software costs are visible, the hidden costs of expertise, training, and ongoing maintenance often exceed initial projections by 200-300%.
Configuration and Implementation Errors
The flexibility that makes self-hosting appealing also creates opportunities for catastrophic misconfigurations. Security experts consistently identify misconfiguration as a leading cause of self-hosted breaches.
Common dangerous misconfigurations include:
- Exposing administrative interfaces to the public internet
- Using default credentials on management systems
- Improperly configured firewall rules
- Inadequate network segmentation
- Missing or misconfigured encryption
- Insufficient logging and monitoring
Example scenario: A startup in Berlin self-hosted their entire application stack on a dedicated server. Their developer, focused on functionality, configured the database to accept connections from any IP address “temporarily” during development. This configuration made it to production and remained undetected for eight months. When discovered after an unrelated security audit, they found evidence that unauthorized actors had accessed their database 47 times, potentially accessing user data, API keys, and proprietary algorithms.
Backup and Disaster Recovery Complexity
Cloud providers invest heavily in redundancy, automated backups, and disaster recovery capabilities. Self-hosters must implement and maintain these systems independently.
Critical considerations include:
- Backup Testing: Untested backups are unreliable backups. How often do you verify restoration procedures?
- Geographic Redundancy: True resilience requires off-site backups, introducing additional complexity and cost.
- Automation: Manual backup processes inevitably fail. Automation requires expertise and ongoing maintenance.
- Encryption: Backup security is as critical as production security, yet often receives insufficient attention.
A financial services firm in Singapore learned this lesson painfully when ransomware encrypted their self-hosted file server. They had backups—but those backups were mounted on the same network and were encrypted along with the production data. The recovery took three weeks, cost $240,000 in consultant fees, and resulted in significant regulatory scrutiny.
The Scale and Sophistication of Modern Threats
Modern cyberattacks have evolved into highly sophisticated, well-funded operations. Research from the University of Maryland indicates that cyberattacks are initiated approximately every 39 seconds worldwide, resulting in over 2,200 attacks daily. Microsoft reported detecting over 600 million hostile signals daily in 2024.
Self-hosted infrastructure faces the same threat landscape as major cloud providers but typically without equivalent defensive resources. Advanced persistent threats, zero-day exploits, and sophisticated social engineering campaigns target all internet-connected systems regardless of hosting model.
Data Breach Landscape in 2026
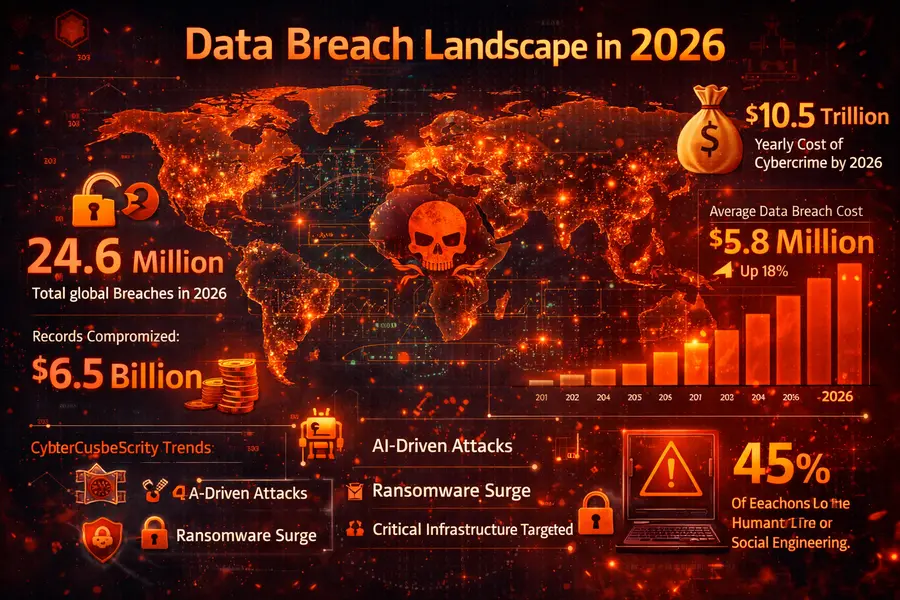
To contextualize these risks, examining current breach statistics provides essential perspective. The data breach landscape in 2026 continues to worsen across all hosting models:
- In the first half of 2025, 1,732 U.S. data breaches exposed 165.7 million records—approximately 95,700 records per breach
- Healthcare remained the most frequently breached industry, with breach costs averaging $7.42 million
- System intrusion accounted for 53% of all breaches
- External actors caused 70% of breaches, while internal actors were responsible for 29%
Perhaps most concerning for self-hosters: ransomware appeared in 23% of data breaches, with the average cost of ransomware incidents remaining high at $5.08 million. Self-hosted environments often lack the sophisticated backup and recovery infrastructure that helps cloud providers mitigate ransomware impact.
A massive credential compilation of nearly 16 billion usernames, emails, and passwords was identified in June 2025, aggregated from infostealer malware logs and previously breached datasets. This treasure trove of compromised credentials presents ongoing risks for any system—self-hosted or cloud—that relies on password-based authentication.
The Hybrid Approach: Balancing Security and Control
Given both compelling benefits and significant risks, many organizations are adopting hybrid approaches that capture advantages of both models while mitigating their respective weaknesses.
Strategic Workload Placement
Rather than making binary self-host-or-cloud decisions, sophisticated organizations strategically place workloads based on specific requirements:
Self-host when:
- Handling extremely sensitive data with regulatory requirements
- Requiring customized security configurations unavailable in cloud offerings
- Dealing with data sovereignty requirements that mandate specific geographic storage
- Operating with predictable, stable workloads where cloud costs become prohibitive
- Possessing the necessary expertise and resources for proper maintenance
Use cloud services when:
- Requiring rapid scalability and elasticity
- Lacking in-house expertise for specialized security requirements
- Needing cutting-edge features that cloud providers implement first
- Operating with variable workloads where cloud elasticity provides cost benefits
- Prioritizing speed to market over complete control
Virtual Private Cloud (VPC) and Dedicated Infrastructure
Hybrid solutions like VPC connectivity and dedicated instances offer middle ground. These provide greater control and isolation than standard cloud offerings while maintaining some cloud benefits:
- Dedicated hardware within cloud provider infrastructure
- Custom network configurations and security policies
- Reduced management overhead compared to complete self-hosting
- Geographic placement control for compliance requirements
A healthcare analytics company in Boston implemented this approach, using self-hosted infrastructure for patient data processing while leveraging cloud services for non-sensitive computational workloads. This architecture allowed them to maintain HIPAA compliance while benefiting from cloud scalability for their research initiatives.
Managed Self-Hosting Services
Emerging managed self-hosting services represent another hybrid model. These services provide self-hosted infrastructure while offering professional management, monitoring, and security services. Examples include managed Nextcloud deployments, managed Kubernetes clusters, and professionally supported open-source applications.
This approach delivers several advantages:
- Greater control than traditional SaaS
- Professional security expertise and monitoring
- Regular updates and patch management
- Still significantly less expensive than pure SaaS in many cases
Best Practices for Secure Self-Hosting
For those committed to self-hosting, implementing comprehensive security practices is non-negotiable. Based on industry standards and expert recommendations from organizations like NIST and OWASP, the following practices are essential:
1. Implement Defense in Depth
Never rely on a single security control. Effective self-hosting security requires multiple overlapping layers:
- Network Security: Properly configured firewalls, network segmentation, VPN access
- Application Security: Regular updates, input validation, secure coding practices
- Access Control: Multi-factor authentication, principle of least privilege, role-based access
- Data Protection: Encryption at rest and in transit, secure key management
- Monitoring: Comprehensive logging, intrusion detection, security information and event management (SIEM)
2. Automate Security Operations
Manual processes don’t scale and inevitably fail. Automation is critical for:
- Patch management and system updates
- Backup execution and verification
- Security scanning and vulnerability assessment
- Log collection and analysis
- Incident detection and response
Tools like Ansible, Terraform, and cloud-init can automate infrastructure configuration and maintenance. For monitoring, solutions like Grafana, Prometheus, and Uptime Kuma provide visibility into system health and security status.
3. Maintain Comprehensive Documentation
Document everything about your self-hosted infrastructure:
- Network diagrams and architecture documentation
- Security configurations and policies
- Incident response procedures
- Recovery procedures and runbooks
- Change management processes
Documentation serves dual purposes: it ensures consistency in security implementation and enables rapid incident response when issues arise.
4. Regular Security Audits and Testing
Periodic security assessments are essential:
- Vulnerability scanning (weekly or more frequently)
- Penetration testing (quarterly or annually depending on risk)
- Configuration reviews (monthly)
- Access audits (quarterly)
- Disaster recovery testing (at minimum annually)
Consider engaging external security professionals for periodic assessments. Fresh perspectives often identify issues that internal teams overlook.
5. Plan for Incidents
Despite best efforts, security incidents will occur. Preparation makes the difference between manageable incidents and catastrophic breaches:
- Develop and document incident response procedures
- Establish communication protocols for security events
- Maintain relationships with security consultants who can assist during incidents
- Practice incident response through tabletop exercises
- Ensure backups are isolated and regularly tested
Self-Hosting vs Cloud Services: Quick Comparison Table
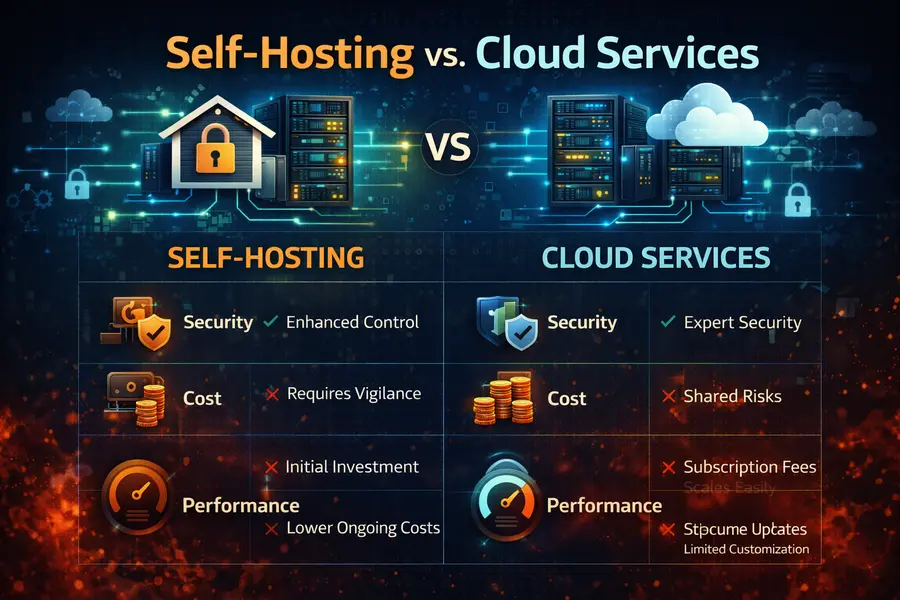
To help visualize the key differences between self-hosting and cloud services, here’s a comprehensive comparison table:
| Factor | Self-Hosting | Cloud Services | Winner |
|---|---|---|---|
| Data Control | Complete ownership and control | Shared responsibility model | Self-Hosting |
| Privacy | Maximum privacy, no third-party access | Subject to provider policies | Self-Hosting |
| Initial Cost | High ($300-$10,000+ for hardware) | Low (pay-as-you-go) | Cloud |
| Long-term Cost | Lower for stable workloads | Can become expensive at scale | Varies |
| Security Expertise Required | Significant in-house knowledge needed | Provider manages most security | Cloud |
| Customization | Unlimited configuration options | Limited to provider offerings | Self-Hosting |
| Scalability | Manual, requires planning | Instant, automatic scaling | Cloud |
| Maintenance Burden | Complete responsibility (5-10 hrs/week) | Minimal user responsibility | Cloud |
| Update Management | Manual, requires vigilance | Automatic, provider-managed | Cloud |
| Compliance Control | Direct control over all requirements | Depends on provider certifications | Self-Hosting |
| Disaster Recovery | Self-implemented and managed | Built-in redundancy and backups | Cloud |
| Performance | Can optimize for specific needs | Shared resources, variable performance | Varies |
| Vendor Lock-in | None, complete portability | Potential dependency issues | Self-Hosting |
| Geographic Control | Complete location control | Limited to provider regions | Self-Hosting |
| Technical Support | Community-based or paid consultants | 24/7 professional support | Cloud |
| Uptime Responsibility | Your infrastructure, your problem | Provider SLA guarantees | Cloud |
| Time to Deploy | Days to weeks | Minutes to hours | Cloud |
| Environmental Impact | Depends on your setup | Optimized data center efficiency | Cloud |
| Best For | Predictable workloads, sensitive data | Variable workloads, rapid scaling | Depends |
Key Takeaway: Neither option is universally superior. Self-hosting excels in data control, privacy, and long-term cost efficiency for stable workloads, while cloud services provide superior scalability, professional management, and lower barrier to entry. Your specific requirements, expertise, and resources should drive the decision.
Making the Decision: Self-Hosting vs. Cloud Services
The choice between self-hosting and cloud services isn’t one-size-fits-all. Several factors should inform your decision:
Organizational Considerations
Team Expertise: Do you have personnel with deep expertise in system administration, security, and network engineering? Can you maintain this expertise long-term through retention and training?
Resource Availability: Beyond initial costs, can you commit to ongoing investment in hardware, software, training, and personnel?
Risk Tolerance: What’s your tolerance for security incidents? Can your organization weather a breach stemming from internal infrastructure failures?
Compliance Requirements: Do regulatory requirements mandate specific controls only achievable through self-hosting? Or do they require capabilities you lack the expertise to implement properly?
Technical Considerations
Workload Characteristics: Are your workloads predictable or variable? Stable or rapidly changing? Self-hosting favors predictable, stable workloads.
Performance Requirements: Do you need ultra-low latency only achievable with on-premises hosting? Or can you benefit from global content delivery networks?
Integration Needs: Does your infrastructure require tight integration with on-premises systems? Or are you building cloud-native applications?
Scalability Requirements: Do you need to rapidly scale resources up or down? Cloud excels here. Or do you operate at consistent capacity where self-hosting is more economical?
Economic Considerations
Total cost of ownership analysis should include:
- Initial hardware and software costs
- Ongoing maintenance and upgrades
- Personnel costs (salary, training, retention)
- Facilities costs (power, cooling, physical security)
- Insurance and liability considerations
- Opportunity costs of staff time spent on infrastructure vs. core business functions
Cloud costs should include all fees—compute, storage, networking, API calls, data transfer—plus the cost of vendor lock-in and potential price increases.
The Future of Self-Hosting in 2026 and Beyond
Several emerging trends are reshaping the self-hosting landscape:
AI-Powered Infrastructure Management
Artificial intelligence is transforming self-hosting from expert-only territory into accessible infrastructure management. AI-powered tools now assist with:
- Automated deployment and configuration
- Predictive maintenance and issue prevention
- Security threat detection and response
- Resource optimization and cost management
These tools don’t eliminate the need for expertise but significantly lower the barrier to entry. A developer with solid general technical knowledge and AI-powered automation can now deploy and maintain infrastructure that previously required specialized system administration expertise.
Edge Computing Integration
Self-hosting is converging with edge computing, enabling new architectural patterns. Rather than centralized cloud or purely on-premises deployments, organizations are distributing workloads across edge locations for optimal performance, cost, and resilience.
Open Source Ecosystem Maturation
The open-source ecosystem supporting self-hosting continues maturing rapidly. Projects like Nextcloud, Bitwarden, Jellyfin, and Home Assistant offer genuine alternatives to commercial SaaS offerings. These aren’t experimental toys—they’re production-ready platforms with active development communities and professional support options.
Sustainability Focus
Environmental concerns are driving interest in efficient self-hosting. ARM-based processors, solar-powered setups, and energy-efficient mini PCs enable sustainable self-hosting with minimal environmental impact. This aligns with broader corporate sustainability initiatives while reducing operational costs.
Conclusion
Self-Hosting in 2026 represents a complex decision matrix rather than a simple binary choice. The security benefits are genuine and substantial—complete data control, customized security implementation, reduced cloud attack surface, and elimination of vendor dependencies. For organizations with appropriate resources, expertise, and requirements, these benefits can outweigh the risks.
However, the security risks are equally real and have led to devastating breaches among organizations that underestimated the challenges. Inadequate patch management, insufficient expertise, configuration errors, and the sophistication of modern threats create substantial vulnerabilities. The data is clear: 60% of breaches stem from missed patches, and the average breach costs millions of dollars.
The most sophisticated approach recognizes that this isn’t an either-or proposition. Hybrid strategies that leverage both self-hosted and cloud infrastructure enable organizations to optimize security, cost, performance, and control based on specific workload requirements.
For those choosing self-hosting, success requires unwavering commitment to security best practices: defense in depth, automation, comprehensive documentation, regular audits, and incident preparedness. Half-measures in self-hosting security create the worst of both worlds—sacrificing cloud benefits while accepting self-hosting risks without proper mitigation.
The self-hosting market’s projected growth to $85.2 billion by 2034 suggests this trend will continue strengthening. As tools improve and expertise becomes more accessible, self-hosting will remain a viable and attractive option for many organizations. The key is approaching the decision with clear-eyed assessment of both benefits and risks, adequate resources and commitment, and realistic expectations about the ongoing investment required for security success.
Disclaimer
This article provides general information about self-hosting security considerations and should not be construed as professional security, legal, or compliance advice. Security requirements vary significantly based on industry, geographic location, regulatory environment, and organizational specifics. Organizations considering self-hosting should:
- Conduct comprehensive risk assessments specific to their environment
- Consult with qualified security professionals before making infrastructure decisions
- Engage legal counsel regarding compliance requirements
- Perform due diligence on all technologies and practices discussed
- Recognize that the cybersecurity landscape evolves rapidly and information in this article may become outdated
The statistics, case studies, and examples cited represent information available as of January 2026. Security practices, threat landscapes, and technological capabilities continue evolving. Readers should verify current information before making decisions based on this content.
Neither the author nor the publisher assumes liability for decisions made based on information in this article. Self-hosting involves inherent risks that each organization must evaluate and manage according to their specific circumstances, risk tolerance, and regulatory obligations.
Frequently Asked Questions
Is self-hosting more secure than using cloud services in 2026?
Security depends more on implementation than hosting model. Self-hosting can be more secure if you have expertise, resources, and commitment to maintain proper security practices. However, for many organizations, major cloud providers offer better security than they could achieve independently. The question isn’t which is inherently more secure, but which model you can execute most effectively given your specific capabilities and requirements.
What are the minimum technical requirements for secure self-hosting?
At minimum, you need: expertise in Linux/Unix system administration, network security fundamentals, experience with firewalls and VPNs, understanding of encryption and access control, capability to implement and maintain backups, and time for ongoing maintenance and monitoring. Most successful self-hosters recommend at least 5-10 hours weekly for maintenance, updates, and monitoring even for small deployments.
How much does self-hosting actually cost compared to cloud services?
Initial self-hosting costs include hardware ($300-$3,000+ depending on requirements), software licenses if using proprietary tools, and significant time investment for setup. Ongoing costs include electricity (typically $15-50 monthly for home servers), internet bandwidth, replacement hardware every 3-5 years, and substantial time for maintenance. Cloud services have predictable monthly fees but can become expensive at scale. Total cost of ownership analysis should include all factors: many organizations find self-hosting more economical for stable workloads while cloud excels for variable usage.
What are the biggest security mistakes self-hosters make?
The most common critical mistakes include: failing to apply security updates promptly, exposing management interfaces to the public internet, using weak or default passwords, neglecting proper firewall configuration, skipping backup implementation or testing, insufficient monitoring and logging, and underestimating the time required for proper maintenance. According to industry data, 60% of breaches result from unpatched vulnerabilities—a directly preventable issue that remains the primary self-hosting security failure.
Can small businesses safely implement self-hosting?
Small businesses can successfully self-host, but should carefully evaluate their capabilities. Success factors include: at least one team member with solid technical expertise and time dedicated to infrastructure management, willingness to invest in learning and tools, realistic assessment of complexity for chosen applications, and commitment to security best practices. Many small businesses find hybrid approaches most practical—self-hosting less critical applications while using managed services for complex systems requiring specialized expertise. Starting small with non-critical applications allows learning before hosting essential business systems.
Also Read
Tails 7.4 Is Out Now: What’s New for Privacy-Focused Linux Users