
Linux Kernel CVE-2026-31431 Explained in Simple Terms
If you’ve been following cybersecurity news this past week, you’ve probably heard the name Copy Fail being thrown around. It sounds almost harmless — but don’t let the name fool you. Linux Kernel CVE-2026-31431 explained in simple terms is exactly what this post aims to deliver, cutting through the technical jargon to tell you what this vulnerability actually is, who it affects, why it matters, and what you should do right now.
Let’s get into it.
What Is CVE-2026-31431 (Copy Fail)?
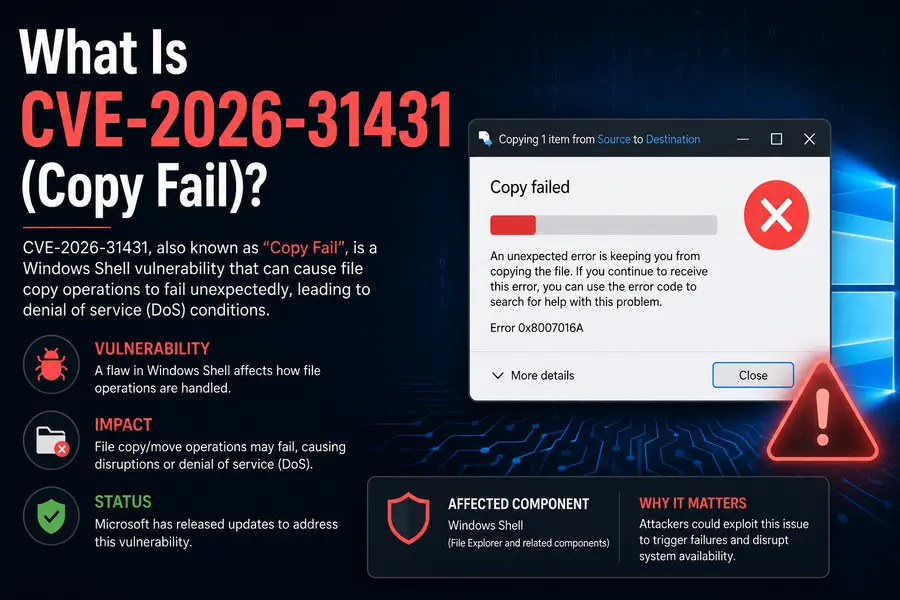
CVE-2026-31431 is a local privilege escalation (LPE) vulnerability in the Linux kernel. Security researchers at the firm Theori discovered and publicly disclosed it on April 29, 2026, after privately notifying the Linux kernel security team five weeks earlier.
The nickname “Copy Fail” gives you a hint about what’s going wrong: the exploit abuses a bug in how the kernel’s cryptographic subsystem copies data — and that failure opens a door straight to root access.
In plain language: a regular, unprivileged user on a vulnerable Linux system can use this flaw to become root — the most powerful account on the machine — without needing any special permissions, passwords, or network access.
It carries a CVSS 3.1 score of 7.8 (High), and it has since been added to the CISA Known Exploited Vulnerabilities (KEV) catalog, with US federal agencies ordered to address it by May 15, 2026.
A Quick Look at the Numbers
Before diving into how it works, here’s a summary snapshot:
| Detail | Value |
|---|---|
| CVE ID | CVE-2026-31431 |
| Nickname | Copy Fail |
| Discovered By | Theori |
| Public Disclosure | April 29, 2026 |
| CVSS Score | 7.8 (High) |
| Affected Kernel Versions | Linux Kernel 4.14 (2017) through 6.19.12 |
| Vulnerability Type | Local Privilege Escalation (LPE) |
| Root Cause |
Logic bug in algif_aead / authencesn crypto module |
Which Systems Are Affected?

This is where the scope of Copy Fail becomes alarming. The bug was introduced in 2017, which means virtually every major Linux distribution released in the past nine years is potentially at risk.
Affected distributions include:
- Ubuntu (all releases before 26.04 Resolute)
- Red Hat Enterprise Linux (RHEL) 10.1
- Debian
- Fedora
- SUSE 16
- Amazon Linux 2023
- AlmaLinux (all supported releases)
- Arch Linux
- CloudLinux
If your system runs a Linux kernel between versions 4.14 and 6.19.12, it is vulnerable. That covers an enormous portion of servers, cloud instances, containers, and developer machines around the world.
How Does the Vulnerability Actually Work?
To understand Linux Kernel CVE-2026-31431 explained in simple terms, you need a tiny bit of background — nothing too deep, I promise.
The Linux Page Cache
When your Linux system loads a file into memory — say, the su command that lets you switch users — it stores that file in something called the page cache. Think of the page cache as a fast, in-memory photocopy of files sitting on your disk. The kernel reads from this cache rather than hitting the disk every single time, which makes things much faster.
Here’s the important part: the physical file on disk doesn’t change when the page cache is modified. And that’s exactly what Copy Fail exploits.
The Crypto Subsystem Bug
The Linux kernel has a feature called AF_ALG (Address Family for Algorithm sockets), which exposes kernel cryptographic functions to userspace applications. It’s the part of the kernel that handles things like hardware-accelerated encryption.
Inside AF_ALG, there’s a module called algif_aead that handles AEAD (Authenticated Encryption with Associated Data) operations — a type of encryption used in protocols like IPsec.
In 2017, a developer introduced an in-place optimization to algif_aead.c (commit 72548b093ee3). The goal was a performance improvement: instead of creating separate source and destination buffers for encryption operations, the code was changed to do the work in a single, combined buffer. It seemed like a reasonable optimization at the time.
However, this change created a subtle but serious interaction with the authencesn cryptographic template (itself added in 2011) and AF_ALG AEAD socket support (added in 2015). The result? Any unprivileged user could use this chain of components to write 4 controlled bytes directly into the kernel’s page cache — specifically, into the in-memory copy of any readable executable file on the system.
The Exploit Chain in Plain English
Here’s how an attacker uses this in practice:
- Target a privileged executable. Most Linux systems have utilities like su, sudo, passwd, and others that run with elevated privileges via the setuid mechanism (meaning they always run as root, regardless of who launches them).
- Corrupt the in-memory copy. Using the AF_ALG interface and the splice() system call, the attacker writes malicious code into the page cache copy of that executable — without touching the file on disk.
- Wait for a privileged process to run. When any privileged process later executes the now-corrupted in-memory version of the file, the attacker’s injected code runs as root.
- Gain full root access. The attacker’s process escalates from a normal user (UID > 0) to root (UID 0), giving them complete control over the system.
What makes this especially nasty:
- No race condition required. Unlike older kernel exploits (like Dirty COW), this doesn’t require winning a timing race. It works deterministically, every single time.
- No disk changes. The exploit leaves no trace on the filesystem. Tools that monitor file integrity (like Tripwire or AIDE) won’t detect a thing.
- No forensic footprint on disk. Because only the in-memory page cache is touched, there’s nothing left behind after a reboot.
- A tiny, portable exploit script. The working proof-of-concept (PoC) is just 732 bytes and works unmodified across essentially all vulnerable distributions.
Why Is Copy Fail Particularly Dangerous in Cloud Environments?
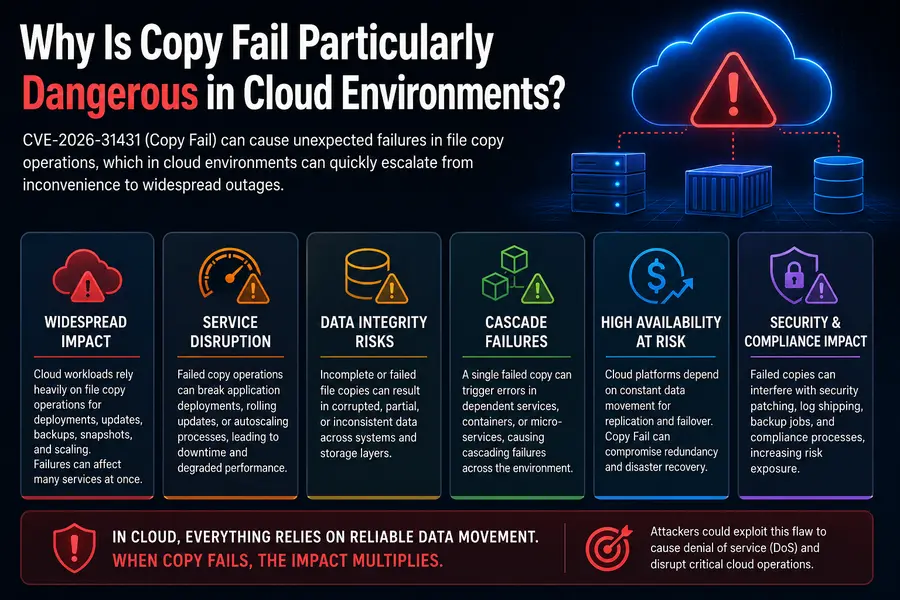
This is where CVE-2026-31431 explained in simple terms gets especially relevant for anyone running infrastructure at scale.
The vulnerability requires local code execution as a regular user — it can’t be used directly over a network. But Microsoft’s security team noted in their analysis that chaining it with any foothold that gets an attacker onto a machine (a web RCE vulnerability, an SSH credential leak, a malicious pull request running on a CI runner) immediately grants them root.
In cloud and Kubernetes environments, where workloads from multiple tenants often share the same underlying nodes, this has serious implications:
- Container breakout — an attacker in a container could potentially escalate and escape to the host
- Multi-tenant compromise — root on a shared node can mean access to every workload running on it
- CI/CD pipeline abuse — attackers who land in a build runner get root, and from there, your secrets and registries
- Lateral movement — root on one node opens pathways across the cluster
Microsoft Defender reported preliminary proof-of-concept testing activity in the wild and warned of likely increased exploitation by threat actors in the days ahead.
What About SELinux and AppArmor?
You might be wondering: “Don’t MAC (Mandatory Access Control) mechanisms like SELinux and AppArmor block this?”
The short answer is: technically yes, but practically no in most setups.
SELinux and AppArmor can prevent untrusted processes from opening AF_ALG sockets — and if they do, the exploit path is blocked. However, in default configurations across most distributions, unconfined or broadly-permitted processes can still access AF_ALG sockets freely. Unless your security policy is specifically hardened to restrict AF_ALG socket access only to explicitly permitted services, the protection is effectively absent.
Red Hat’s guidance recommends ensuring SELinux is in enforcing mode and using default Security Context Constraints — but notes this alone isn’t sufficient without additional kernel-level patching or module disabling.
The Patch Status: Where Things Stand as of May 7, 2026
The upstream Linux kernel fix was merged as commit a664bf3d603d, which simply reverts the 2017 in-place optimization that introduced the bug. It’s a clean, targeted fix.
Here’s the current state across distributions:
| Distribution | Status |
|---|---|
| Arch Linux | Patched at time of disclosure |
| Fedora | Patched at time of disclosure |
| Amazon Linux | Patched at time of disclosure |
| Ubuntu | Kernel packages with fix released; mitigation available via kmod update |
| Debian | Patched kernel packages available |
| AlmaLinux | Patched kernels in production repositories as of May 1 |
| SUSE 16 | Mitigation guidance released April 30; patches rolling out |
| Red Hat Enterprise Linux | Mitigation guidance released April 30; kernel patches still in progress |
| CloudLinux | Patches available |
CISA added Copy Fail to its KEV catalog on May 4, 2026, with a remediation deadline of May 15, 2026 for US federal civilian agencies.
What Should You Do Right Now?
Option 1: Apply the Kernel Patch (Recommended)
The best fix is a full kernel update. Run the appropriate update command for your distribution:
sudo apt update && sudo apt upgrade
sudo rebootsudo dnf clean metadata && sudo dnf upgrade
sudo rebootsudo pacman -Syu
sudo rebootsudo zypper update
sudo rebootOption 2: Disable the algif_aead Module (Interim Mitigation)
If you can’t reboot or apply a patch immediately, you can disable the vulnerable kernel module. This removes the attack surface while you prepare to patch:
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
sudo rmmod algif_aeadNote: On some Amazon Linux 2 ARM64 systems where the module is built into the kernel, use this approach instead, followed by a reboot:
sudo grubby --update-kernel ALL --args "initcall_blacklist=algif_aead_init"
sudo rebootBe aware of one tradeoff: Disabling algif_aead removes hardware-accelerated AEAD cryptography. Applications that rely on this module should gracefully fall back to software-based cryptography, but some may not. Test this in non-production environments first, particularly in workloads involving IPsec, VPN, or encryption-heavy services.
Other Hardening Steps
- Disable SSH access where it isn’t needed
- Ensure SELinux or AppArmor is in enforcing mode
- Run workloads as non-root users where possible
- Audit which users have local shell access on shared hosts
- In Kubernetes environments, restrict oc debug access to trusted cluster administrators
Timeline of Key Events
Here’s a quick chronological overview of how this vulnerability unfolded:
- 2011: authencesn cryptographic template added to the Linux kernel
- 2015: AF_ALG AEAD socket support introduced
- 2017 (commit 72548b093ee3): In-place optimization added to algif_aead.c — the root cause of Copy Fail
- ~March 24, 2026: Theori privately discloses the vulnerability to the Linux kernel security team
- April 29, 2026: Public disclosure by Theori; working PoC released; some distros already patched
- April 30, 2026: SUSE, Red Hat, and Ubuntu release mitigation guidance
- May 1, 2026: AlmaLinux patches in production repositories
- May 4, 2026: CISA adds CVE-2026-31431 to the KEV catalog
- May 15, 2026: CISA deadline for US federal agencies to remediate
Frequently Asked Questions
Can this be exploited remotely?
No. CVE-2026-31431 requires local access — the attacker needs to already have a shell on the machine as a regular user. However, chaining it with a remote code execution vulnerability makes it a two-step path to root.
Does rebooting fix it?
A reboot clears the corrupted page cache and removes the immediate threat, but it does not patch the underlying vulnerability. The system remains exploitable after a reboot unless you apply the kernel update or disable the module.
Will my antivirus or file integrity monitor catch this?
No. Because the exploit only modifies the in-memory page cache and doesn’t write anything to disk, traditional file integrity monitoring tools will not flag it. This is one of the most dangerous aspects of Copy Fail.
Is there active exploitation in the wild?
As of early May 2026, exploitation has been primarily observed in proof-of-concept testing. However, Microsoft Defender warned of likely increased threat actor activity as the PoC is publicly available and trivial to use. The CISA KEV listing confirms it is being treated as an actively exploited threat.
Does this affect Android?
Android uses the Linux kernel but is a different platform with its own security model. Most consumer Android devices do not expose AF_ALG sockets to unprivileged apps. However, system administrators should assess their specific Android-based embedded or enterprise deployments independently.
The Bigger Picture
Copy Fail is a reminder that security bugs don’t always look like bugs when they’re introduced. The 2017 commit that caused this was a reasonable performance optimization made in good faith. The three separate kernel changes that combined to create this vulnerability — added in 2011, 2015, and 2017 — each made sense in isolation. It was only their interaction, discovered years later, that revealed the flaw.
What makes Linux Kernel CVE-2026-31431 explained in simple terms so important as a case study isn’t just the severity — it’s the nature. This is a deterministic, disk-silent, forensic-trace-free privilege escalation that works on nine years’ worth of Linux systems. It’s not a corner case or a theoretical attack. The exploit is 732 bytes, public, and works reliably every time.
The good news is that patches are out, mitigations are available, and the community response has been fast. Distros like AlmaLinux, Fedora, and Arch had fixes ready at or before public disclosure. The fix itself is clean — revering a single optimization commit — and carries minimal risk.
Patch your systems. Disable the module if you can’t patch immediately. And treat local access controls as seriously as network access controls.
If you manage Linux systems at any scale — a single VPS, a fleet of cloud servers, or a Kubernetes cluster — this is one of those vulnerabilities where speed genuinely matters.
Disclaimer
The information provided in this article is for educational and informational purposes only. While every effort has been made to ensure accuracy based on publicly available data as of May 2026, the vulnerability landscape changes rapidly. Always refer to your distribution’s official security advisories and patch notes for the most current guidance. The author is not responsible for any actions taken or not taken based on the content of this post. If you manage production systems, consult a qualified security professional before making changes.
Related Linux Articles
-
Manjaro 26.1 Bian-May Preview Goes Live
Explore the latest Manjaro 26.1 preview featuring GNOME 50, KDE Plasma 6.6, Xfce 4.20, and Linux Kernel 7.0. -
EndeavourOS Titan Neo Review
A detailed look at EndeavourOS Titan Neo performance, stability improvements, installer updates, and new Linux features. -
The Most Obscure Linux Distros That Actually Work
Discover unique and underrated Linux distributions that offer surprisingly stable and useful experiences.




